With mid-size businesses accounting for 43% of cyberattacks, building robust cyber defense solutions to protect customer and organization data is becoming a universal imperative. Worryingly, only 14% of SMBs have the cybersecurity needed to sustain attacks that are on the rise.
If yours is among the businesses that are yet to reinforce their defenses, doing so requires increasing urgency as threats evolve.
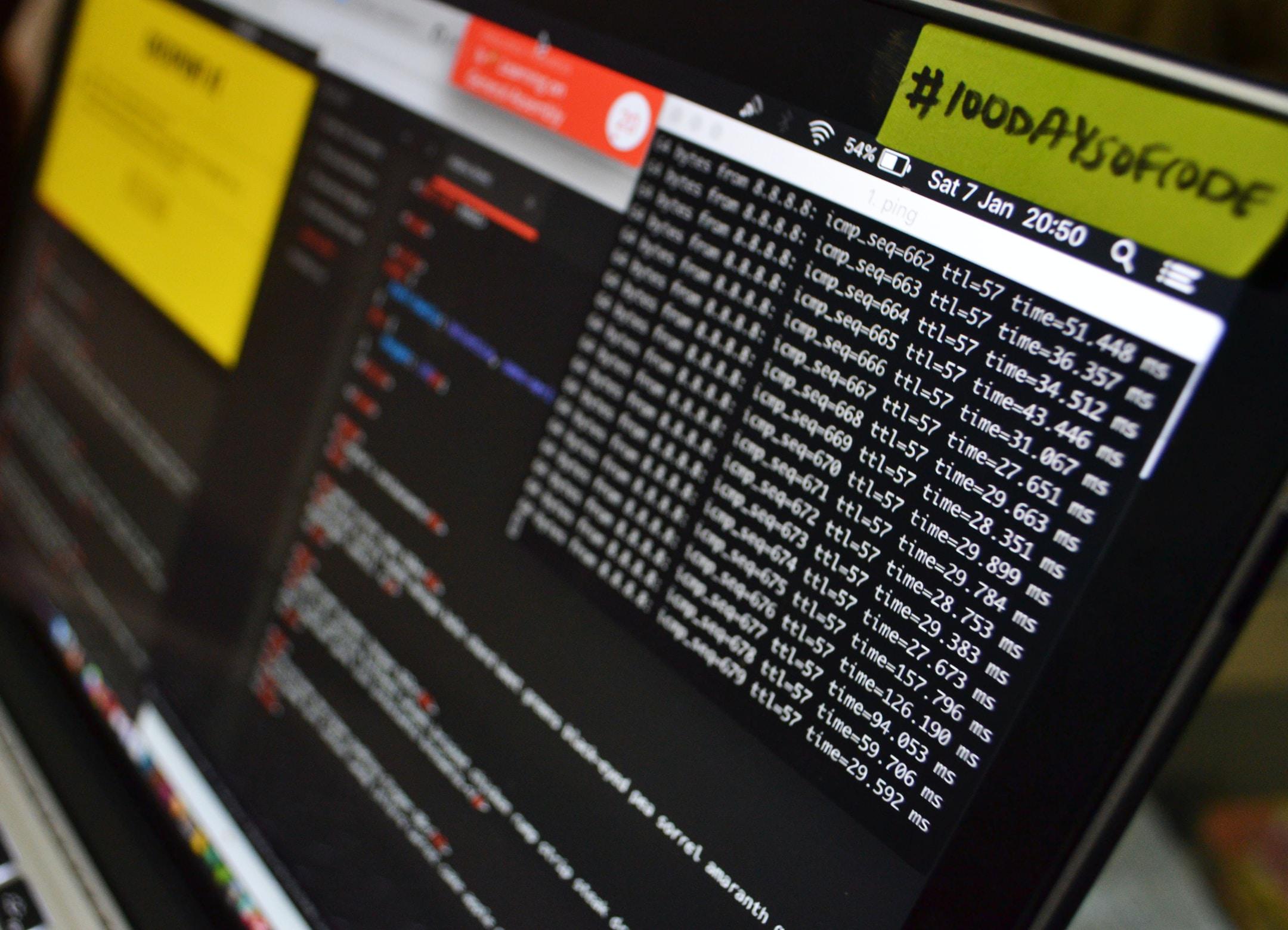
Our experience with cybersecurity at Baran Agency includes working with businesses across different industries, including some within the Defense Industrial Database. As a result, our approach to cybersecurity is necessarily modern, precise, and thorough.
We recommend that you follow these four practices as you fortify your systems.
If your business is to be attacked, the firewall is among the first lines of defense. The FCC advises all small and medium-size businesses to install one for added protection against breaches.
In addition to the standard external firewall, you may also wish to install an internal version for enhanced security within the system.
Businesses that have shifted vital operations to the cloud are best protected when they also deploy their firewall across the cloud.
And if you have plans to work with the Department of Defense, take note that your firewall needs to be up to significantly higher standards than one used for purely civilian purposes.
In most cases, you’ll have to upgrade various components of your security framework until you qualify for ISO certification.
The Baran Agency works extensively with DoD contractors. So, if this is something you may need us to walk you through in detail and in the context of your business, our industry specialists can gladly set up a meeting.
Research by global anti-malware firm, Kaspersky, reveals that 47% of small and medium business leaders feel that employees are their largest cybersecurity vulnerability. Supporting this outlook, work-from-home policies have led to more breaches in 20% of surveyed organizations.
As you begin installing your defenses, you must consider measures that limit your business’ exposure to poor employee conduct. One of the most severe threats you will need to prepare for is phishing, which is the most common way for intruders to gain access into protected systems.
A simple solution you may wish to try is multi-factor authentication. It ensures that even if an employee’s device or password is compromised, a hacker can’t access the employee’s accounts without compromising a secondary device, password, or entry method. The chances of that happening are very slim.
Even if hackers manage to access your system, anti-malware mitigates risk by minimizing the harm intruders can do. For example, hackers cannot easily install malicious programs that corrupt organizational data.
Similarly, anti-malware prevents cybercriminals from embedding themselves within the system, ensuring continued access even after your IT admin takes action.
Once cybercriminals breach an organization’s system, they may attempt to corrupt the data or do so unintentionally. Or, your business may shut down certain components of the system to limit unauthorized access, posing a risk to your data.
In each situation, efficient backup systems are essential for business continuity and avoiding costly loss of records.
Your organization can maintain high bandwidth while regularly backing up data with integrations that maximize resource usage.
The Baran Agency is headed by veterans, cybersecurity professionals with extensive and decorated military backgrounds, and compliance officers. Our blend of expertise enables us to offer CaaS (compliance as a service) that meets military standards and provides class-leading robust protection.
Contact us today for effective cyber defense solutions that protect your organization and stakeholders and ensure compliance.